Saturday, September 13, 2003
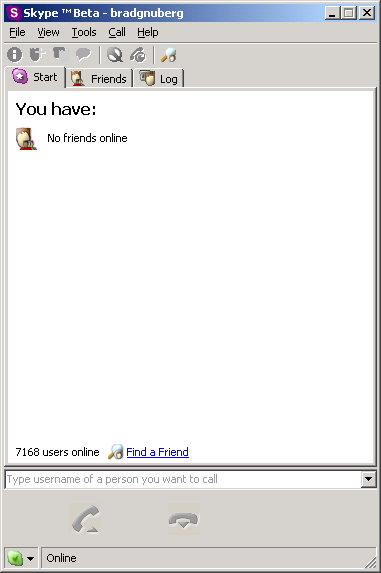
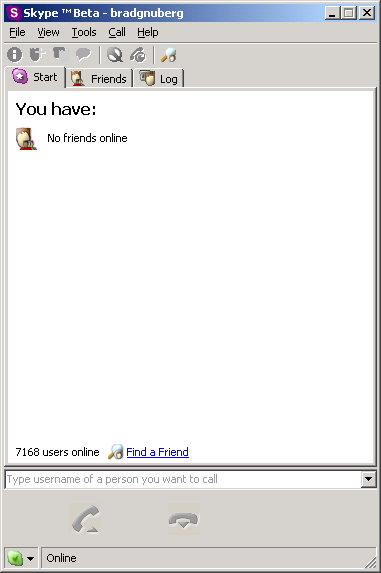
Here's a screen shot of Skype, the new P2P VoIP tool from the makers of Kazaa:
"What other differences does a P2P telephone system have over others out there?"
"P2P telephony just works. Our research shows that more than 50 percent of broadband users are behind NAT (network address translation) and firewalls and can therefore not make full use of VoIP solutions that are based on SIP (Session Initiation Protocol). The P2P technology we use makes it possible to connect and receive calls, as long as you can make an outgoing Internet connection. People expect telephony to be simple. You pick up the handset; you get a dial tone; you call. That kind of simplicity is our benchmark."
See the full interview
"P2P telephony just works. Our research shows that more than 50 percent of broadband users are behind NAT (network address translation) and firewalls and can therefore not make full use of VoIP solutions that are based on SIP (Session Initiation Protocol). The P2P technology we use makes it possible to connect and receive calls, as long as you can make an outgoing Internet connection. People expect telephony to be simple. You pick up the handset; you get a dial tone; you call. That kind of simplicity is our benchmark."
See the full interview
Posted two articles on the JXTA P2P Sockets web site:
Introduction to Peer-to-Peer Sockets
How to Create Peer-to-Peer Web Servers, Servlets, JSPs, and XML-RPC Clients and Servers
Introduction to Peer-to-Peer Sockets
How to Create Peer-to-Peer Web Servers, Servlets, JSPs, and XML-RPC Clients and Servers
I've been reading up on Identity Based Encryption (IBE) lately. Basicly, this is a subset of cryptography that is trying to get around the problems with standard public-key infrastructures (PKI). In Identity Based Encryption, any string can be used to generate a public key, such as using an email address or a username. The great thing about this is that now any person can figure out what my public key is from some well-known string, such as "BradGNUberg", without having to consult a public-key infrastructure. I'm interested in this because I am a P2P hacker, and I've been trying to figure out ways to do an end-run around Zooko's Triangle, which basicly states that you can't have a naming system that is decentralized, secure, and human-friendly all at the same time. I've currently built a light-weight domain name system in the JXTA P2P Sockets project, but it is not secure.
Some IBE resources I've found:
Some other interesting papers I found while trolling for IBE stuff:
Secure Communication in a Distributed System Using Identity Based Encryption
USING IDENTITY-BASED ENCRYPTION TO ELIMINATE CERTIFICATES IN SSL TRANSACTIONS
Some IBE resources I've found:
- IBE Secure E-mail - "The cryptosystem has chosen ciphertext security in the random oracle model assuming an elliptic curve variant of the computational Diffie-Hellman problem." More info in the publication Identity based encryption from the Weil pairing. I think this has patent issues.
- Terence Spies on Identity-Based Encryption - Interview with someone at Voltage Security, "a new company that hopes to make encryption more useful and usable."
- Voltage Security - "a new company that hopes to make encryption more useful and usable." I think it's based on the Weil pairing scheme: "In 2000, Dr. Dan Boneh and Dr. Matt Franklin achieved a mathematical breakthrough and invented the first practical Identity-Based Encryption (IBE) system. Their scheme uses bi-linear mappings, known as Weil and Tate pairings, on elliptic curves to obtain an algorithm that can be used to turn a simple, well recognized identity into a public/private key pair. From these powerful mathematics comes an elegant mechanism for securing business communication � online and offline, without the need to pre-register recipients."
- http://ntrg.cs.tcd.ie/~argp/ibe.html - "This page contains a list of resources (research papers, applications, links, etc.) concerning identity-based encryption (IBE)."
Some other interesting papers I found while trolling for IBE stuff:
Secure Communication in a Distributed System Using Identity Based Encryption
USING IDENTITY-BASED ENCRYPTION TO ELIMINATE CERTIFICATES IN SSL TRANSACTIONS
Subscribe to Posts [Atom]
